Featured
Table of Contents
- – What Is The Wireguard Vpn Protocol?
- – Vpn Protocols: Openvpn Vs Ipsec, Wireguard, L2...
- – Nordlynx Vs Openvpn: Pros And Cons (2022)
- – Ipsec Vs Openvpn: Which One Should You Use?
- – What Is A Vpn? How Does It Work And Why Do Yo...
- – What Is Openvpn And Should You Use It?
- – Openvpn
- – Openvpn Vpn Protocol
What Is The Wireguard Vpn Protocol?
As soon as you have installed the app on the devices, move on to step 5. Now you just require to import the certificates and secrets already produced in the steps above. To do this, merely follow these steps: Copy the ca.
It's one of the safest procedures. If you go for a third-party VPN service, it's recommended that you choose a service provider that offers it in order to enjoy an extremely safe online experience without fear of hackers. We hope this guide responds to all concerns about how Open, VPN works, how to set it up and when you ought to utilize it.
The first thing to understand about Open, VPN is that it is a VPN procedure. A procedure is a set of rules that. It determines how to encrypt and identify data packets passing throughout VPN connections.
Vpn Protocols: Openvpn Vs Ipsec, Wireguard, L2tp, & ...

Open, VPN's open-source community checks bugs and fine-tunes the protocol, including new features and upgrading security components. Continuous analysis means that the protocol is.
Open, VPN systems can serve a single workstation linking to a company network or scale as much as enterprise-wide security systems. The VPN is created to cover as lots of devices as users require. Users download pre-configured customers, install them to their gadgets, and are ready to go. Among the greatest Open, VPN advantages is that users can set up Open, VPN clients on Windows, Linux, and mac, OS.
Users won't require to trust that corporations protect data and prevent security errors. A worldwide coding community fine-tunes Open, VPN to respond to the latest cybersecurity trends. The advantages noted above different Open, VPN from the majority of other VPN protocols. No cybersecurity technology is flawless. Open, VPN is no exception, and there are several potential weak points users require to understand about:.
Nordlynx Vs Openvpn: Pros And Cons (2022)
This is hassle-free, but business with bespoke security requirements might discover other protocols more user-friendly. Open, VPN has actually ended up being a structured service for desktop and laptop operating systems but is not as slick for mobile users. Android and i, OS applications are not as innovative or user-friendly, although they are enhancing all the time.
Due to the fact that UDP does not have a handshake process,. It is possible to lose information throughout transmission, making UDP less ideal for organization situations where precise transfers are necessary. Transmission Control Protocol (TCP) is the other Open, VPN mode. In this case, TCP is classified as a stateful protocol. This implies that the server maintains information about the session state.
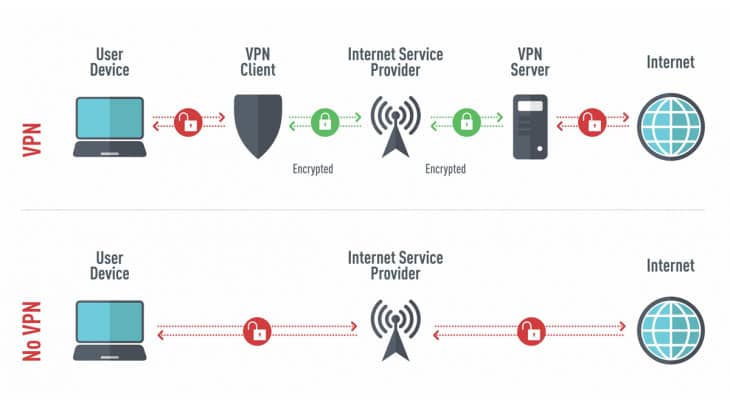
You might think Open, VPN is a type of VPN. Well. It's not. So, what is Open, VPN? How does it work? And why should you even care? We have all the answers. A VPN is a tool that lets you browse the web with some degree of privacy. It encrypts your web traffic information and routes it to a remote server, changing your IP address in the procedure.
Ipsec Vs Openvpn: Which One Should You Use?
Point-to-Point Tunneling Procedure is a prime example. Stability is the calling card of others. Internet Secret Exchange v2 is a great case in point. However the most popular ones are extremely configurable for a range of uses - you can make them as secure and lightweight as the need develops.
Hotspot Guard relies on absolutely nothing however its exclusive Catapult Hydra. It used to support Open, VPN and IPSec (Web Procedure Security), but Anchor, Free Inc. (its developer) felt both procedures had inappropriate latency concerns. In time, new tunneling protocols occur to take it up a notch. At the minute, Wire, Guard is the talk of the town.
The Open, VPN protocol can be a pain to configure by hand. Its complexity, its only unassailable disadvantage, can make your head swim. TCP and UDP Open, VPN procedures are usually preconfigured in a lot of VPN apps for personal usage. Speaking of which, almost all of the VPNs we have actually checked support Open, VPN.
What Is A Vpn? How Does It Work And Why Do You Need ...
Besides Hotspot Guard, Hola VPN was the only other supplier we have actually come across that didn't use Open, VPN. Still, some of the most popular VPN services - like PIA, Surfshark, Nord, VPN, and Express, VPN - support it. Open, VPN is one of the very best all-around VPN protocols out there.
Without a doubt, Open, VPN technologies are safe. It's no longer the very best at a lot of things with the introduction of Wire, Guard. Open, VPN stays a good option for streaming, torrenting, and personal web browsing.
Over the past couple of years, Virtual Private Networks (VPNs) have actually ended up being an incredibly popular approach for securing yourself while utilizing the web. There's a variety of VPN providers out there, such as Nord, VPN, Surf, Shark, and Express, VPN, but you might not have actually found out about the technology they use.
What Is Openvpn And Should You Use It?
Open, VPN is an open source connection procedure that uses encryption and authentication to develop a secure "tunnel" in between the user and the server. You may have heard popular VPN companies use this kind of example when explaining their service, and that's because numerous of them use Open, VPN to offer you with online security.
This is one of the Open, VPN's key security elements, and stands as one of the most secure encryption methods out there today. On top of all this, Open, VPN is open source, implying that anyone can view the code, which any bugs can be identified and repaired quickly by the Open, VPN community if the designers do not see to it initially.
How do you in fact use it? At this moment, you may be thinking, "if Open, VPN is so excellent, why have not I heard of it prior to?". Well, Open, VPN is the technology used by much of the leading VPN service providers you understand of, such as Browse, Shark, Personal, VPN, and Express VPN.
Openvpn
What many don't understand is that Open, VPN, unlike the other providers pointed out above, is totally complimentary to utilize, suggesting you'll never ever have to handle any in advance charges or subscription charges. But can Open, VPN be used as quickly as popular providers simply by itself? Related: How to Establish a VPN in Windows 11 You can utilize Open, VPN personally, it is more geared towards businesses that have lots of people connecting to a server at once.
This is another VPN protocol that can offer a more reputable connection and has a more safe kind of file encryption. Only time will tell whether this procedure ends up being the next big thing in online security. While it's easy to register for a subscription-based VPN service with simply a few clicks of the mouse, you might desire to think about giving Open, VPN a go if you desire the exact same technology without an in advance or month-to-month charge.
To have the Open, VPN procedure discussed, we 'd state it's the most versatile of them all. Open, VPN Community Edition is the standard, free version of the software application, while Open, VPN Gain Access To Server is the sophisticated, paid variation.
Openvpn Vpn Protocol
One of the strengths of Open, VPN is that it can be utilized on both User Datagram Procedure (UDP) and Transmission Control Protocol (TCP). These are the interaction standards that make it possible for gadgets to exchange messages over the network. From what we have actually experienced, Open, VPN with TCP is more reliable, while Open, VPN with UDP appears to be much faster.
Open, VPN is among the best VPN protocols on the marketplace. The primary factor for that is that it's an open-source option, and no business owns or runs it. You can be totally sure your data is safely sent, and no one can get unapproved access to it or sell it to a third celebration.
Table of Contents
- – What Is The Wireguard Vpn Protocol?
- – Vpn Protocols: Openvpn Vs Ipsec, Wireguard, L2...
- – Nordlynx Vs Openvpn: Pros And Cons (2022)
- – Ipsec Vs Openvpn: Which One Should You Use?
- – What Is A Vpn? How Does It Work And Why Do Yo...
- – What Is Openvpn And Should You Use It?
- – Openvpn
- – Openvpn Vpn Protocol
Latest Posts
Best Virtual Private Network (Vpn) Software 2023
The Best Vpn For Business In 2023: Top 8 Corporate ...
Best Vpns For Freelancers And Remote Workers: Protect ...
More
Latest Posts
Best Virtual Private Network (Vpn) Software 2023
The Best Vpn For Business In 2023: Top 8 Corporate ...
Best Vpns For Freelancers And Remote Workers: Protect ...